Network Configuration Assurance With NetBox and Ansible
In a recent webinar we explored how to get started with Network Automation using NetBox and Ansible, and one of the tasks we automated was backing up network device configuration files. We then took that one step further and compared the running configuration file ie. the actual state of the device with the intended state as defined in NetBox, and then reported on any differences between the two states. This is a really powerful use case for network automation and this blog post takes a deeper dive into the solution.
Subscribe to our community newsletter for more tutorials like these!
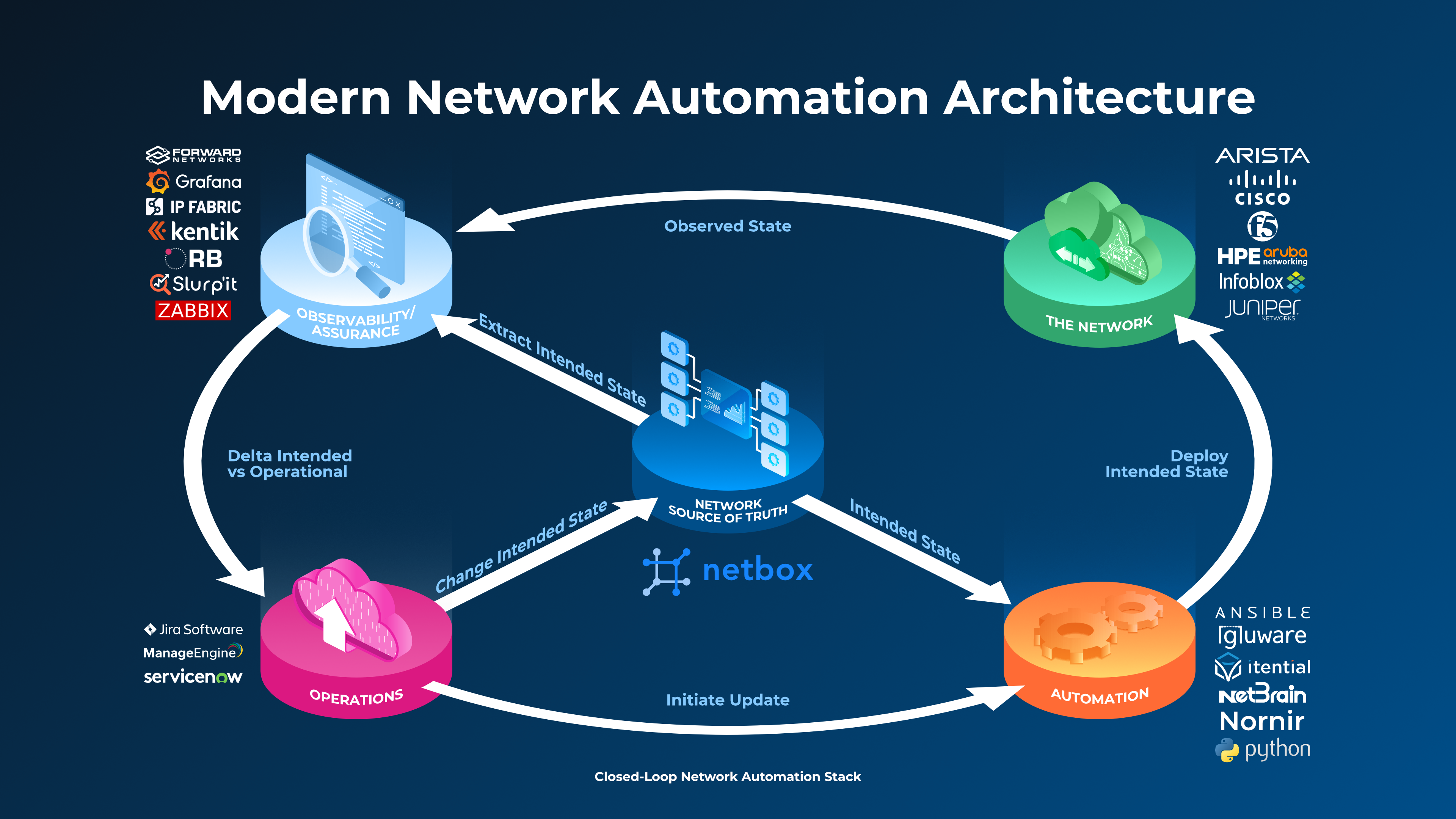
To set the scene this diagram illustrates where both tools fit into a modern network automation reference architecture. You will note that NetBox is at the centre as the Network Source of Truth (NSoT) and defines the intended state, and Ansible (bottom right) is an automation platform that extracts the intended state from NetBox and uses it to perform its automation tasks.
Note that in the diagram other tools in the top-left corner are performing observability and assurance tasks (comparing intended and actual states), but in this example we are going to leverage Ansible in that role also. This is a reference architecture after all so you can find some tools performing multiple roles:
The Intended State – NetBox
We are using containerlab for our network, and have three Arista cEOS switches modelled in NetBox at a site called ContainerLab. Each device is has an IPv4 management IP address and has 3 VLANs defined (100, 200 and 300) that are linked to the site:


For illustrative purposes, we have a simple config template (written in the Jinja templating language) for the devices and this is stored in a remote data store (Git repository), which is synchronized with NetBox. When you click on the Render Config tab of each device you can see the rendered configuration, built using device the data from NetBox, and this is the intended state of each of the network device configurations:

NetBox as a Dynamic Inventory for Ansible
By using the NetBox Inventory Plugin for Ansible we can integrate the two tools seamlessly so that Ansible gets all its inventory data from NetBox:

The example code for this is in the accompanying Git repo, but there are two files that we are interested in. The first one is ansible.cfg which tells Ansible where to look for it’s inventory data:
And the second one is netbox_inv.yml which uses the netbox.netbox.nb_inventory plugin. This file is highly configurable as per the documentation, and in this example we are mapping the slug of the OS from NetBox to the ansible_network_os and grouping our devices by device_roles, sites and platforms:
If we run the command ansible-inventory -i netbox_inv.yml --list to list the inventory, we can see what is returned. I’ve limited the output here just to show the contents of the group sites_container_lab which contains our three target devices:
Ansible Playbook Structure
Following best practices that make our code re-usable, our ansible playbooks are split into Roles for each of the functions that we are automating, and our file structure looks as follows:
Each role has a tasks/main.yml file that contains the playbook code, and a vars/main.yml file that contains any variables that the playbook will reference when it executes. Let’s explore the code for each Role:
role: ACTUAL_STATE
The purpose of this role is simply to collect the running configuration (actual state) from each device and then store this in a file for use by a later playbook. The only variable we are using in this play sets the path for the backups directory where we will store the running configuration of each device:
The playbook itself uses the eos_command module to execute the show running-config command against each device (play 1), then creates the main backup folder (play 2), creates a folder for each device (play 3) and then copies the output from play 1 ie. the running config to a file in the device folder for each device (play 4). This file is called {{ inventory_hostname }}_running.conf:
role: INTENDED_STATE
The purpose of this role is to query NetBox (remember it’s the source of truth) for the intended state of each device and then store this in a file to be compared against the actual config in a later play. Starting with the variables used, we are setting the URL of the NetBox instance and the API token we are using to connect to it, as the values we have set in our system environment (see git repo for instructions), and we are setting the directory that we will store the intended configurations in:
The playbook itself makes an API call to retrieve the details for each device from NetBox (play 1), then makes another API call that uses the device id (from play 1) and renders the intended configuration of each device (play 2), then creates the main folder (play 3), creates a folder for each device (play 4) and then copies the output from play 1 ie. the intended config to the device folder for each device (play 5). This file is called {{ inventory_hostname }}_intended.conf:
role: COMPARE_STATES
The purpose of our final role is to compare the two files generated for each device by the playbooks in the ACTUAL_STATE and INTENDED_STATE roles and report on any differences. Let’s break it down:
Firstly we set variables for the paths to the actual and intended config files for each device, and define a Regex pattern that will be used to exclude parts of the file text that we don’t want to check when we compare the files:
The playbook itself creates a temporary file containing the actual (running) configuration for each device (play 1) then removes any lines that match the regex exclusion_pattern from the temporary file (play 2), then compares the file with the intended configuration file (play 3), then if there is a difference between the two files it displays it to the console output (play 4), and finally it cleans up by removing the temporary files.
Putting it All Together
OK, if you’ve made it this far you’re obviously interested in how it all plays out, so let’s take a look! For demo purposes I have deleted VLAN 300 from the running configuration of ceos-sw-3:
We have a master playbook called compare_intended_vs_actual.yml which calls the other playbooks in the roles we have outlined above, and targets the devices at the ContainerLab site:
We’ll run this with the command ansible-playbook compare_intended_vs_actual.yml. The full output is quite long as there are a lot of plays being run, so I will limit the output to just the interesting parts. The action starts at play 3 in the COMPARE_STATES role, where the play fails when it compares the intended state to the actual state for device ceos-sw-3 and spots that there is a difference. The next task then displays the missing part of the configuration on ceos-sw-3 in the console output:
So you can now clearly see that the actual state of device ceos-sw-3 does not match the intended state as defined by NetBox, and we can now do something about that – ideally using automation tools to push out the intended state to the device!
NetBox and Ansible Resources for Configuration Assurance
So, I hope that this has been a useful overview of how you can build a simple network configuration assurance workflow using NetBox and Ansible. You can try this out yourself as all the code (including the containerlab definition file) is in the accompanying Git Repository.
Also, if you would like to watch the full webinar that this blog post is based on then it is available to watch on-demand, and if you are interested in receiving tutorials like this in your inbox, subscribe to our community newsletter.
Learn more about NetBox Assurance, which identifies and helps you resolve differences in network configuration.
